Network Protocol - Types of Network Protocols
What is a Network Protocol
Standardized network protocols are important for providing a common language so that the network devices can successfully send and receive information. Rules of network protocol include guidelines that regulate the following characteristics of a network: access method, allowed physical topologies, types of cabling, and speed of data transfer. One of the most popular models that are used to build open communication between two network systems is the Open Systems Interconnection (OSI) model.
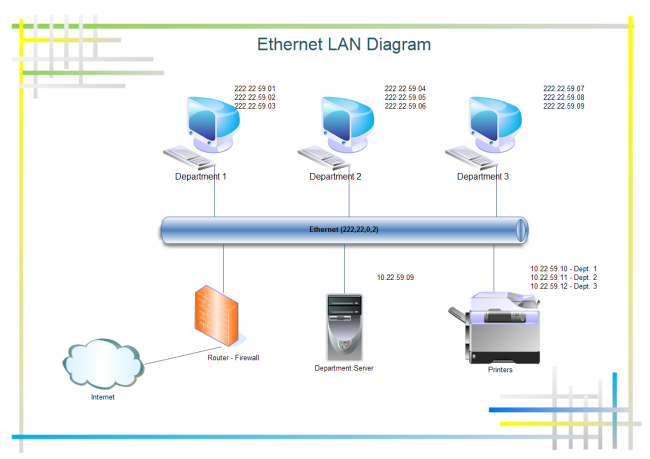
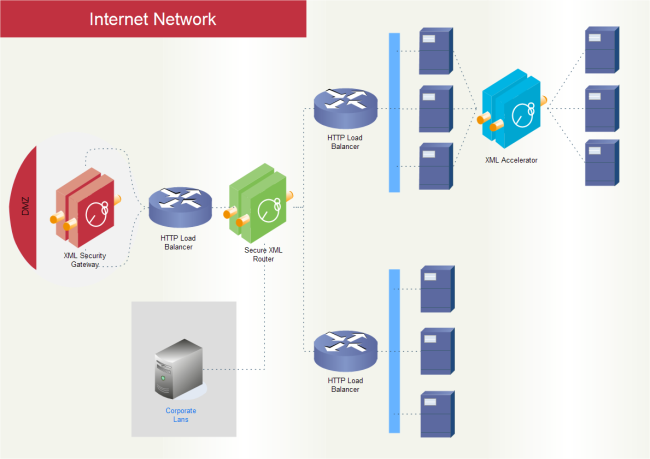
The followings are some commonly used network symbols to draw different kinds of network protocols.

Types of Network Protocols
The most common network protocols are:
- Ethernet
- Local Talk
- Token Ring
- FDDI
- ATM
Ethernet
The Ethernet protocol is by far widely used. Ethernet uses an access method called CSMA/CD (Carrier Sense Multiple Access/Collision Detection). It is a system where each computer listens to the cable before sending anything through the network. If the network is clear, the computer will transmit. If some other nodes have already transmitted on the cable, the computer will wait and try again when the line is clear. Sometimes, two computers attempt to transmit at the same instant. A collision occurs when this happens. Each computer then backs off and waits a random amount of time before attempting to retransmit. With this access method, it is normal to have collisions. However, the delay caused by collisions and retransmitting is minimal and does not normally affect the speed of transmission on the network.
The Ethernet protocol allows for linear bus, star, or tree topologies. Data can be transmitted over wireless access points, twisted pair, coaxial, or fiber optic cable at a speed of 10 Mbps up to 1000 Mbps.
Fast Ethernet
To increase the speed of transmission, the Ethernet protocol has been developed a new standard that supports 100 Mbps. It is commonly called Fast Ethernet. Fast Ethernet requires the application of different, more expensive network concentrators/hubs and network interface cards. In addition, category 5 twisted pair or fiber optic cable is necessary. Fast Ethernet is becoming common in schools that have been recently wired.
Local Talk
The Local Talk is a network protocol that was developed by Apple Computer, Inc. for Macintosh computers. The method used by Local Talk is called CSMA/CA (Carrier Sense Multiple Access with Collision Avoidance). It is similar to CSMA/CD except that a computer signals its intent to transmit before it does so. Local Talk adapters and special twisted pair cable can be used to connect a series of computers through the serial port. The Macintosh operating system allows the establishment of a peer-to-peer network without the need for additional software. With the addition of the server version of AppleShare software, a client/server network can be established.
The Local Talk protocol allows for linear bus, star, or tree topologies using twisted pair cable. A primary disadvantage of Local Talk is low speed. Its speed of transmission is only 230 Kbps.
Token Ring
The Token Ring protocol was developed by IBM in the mid-1980s. The access method used involves token-passing. In Token Ring, the computers are connected so that the signal travels around the network from one computer to another in a logical ring. A single electronic token moves around the ring from one computer to the next. If a computer does not have information to transmit, it simply passes the token on to the next workstation. If a computer wishes to transmit and receives an empty token, it attaches data to the token. The token then proceeds around the ring until it comes to the computer for which the data is meant. At this point, the data is captured by the receiving computer. The Token Ring protocol requires a star-wired ring using twisted pair or fiber optic cable. It can operate at transmission speeds of 4 Mbps or 16 Mbps. Due to the increasing popularity of Ethernet, the use of the Token Ring in school environments has decreased.
FDDI
Fiber Distributed Data Interface (FDDI) is a network protocol that is used primarily to interconnect two or more local area networks, often over vast distances. The access method used by FDDI involves token-passing. FDDI uses a dual ring physical topology. Transmission usually occurs on one of the rings; however, if a break occurs, the system keeps information moving by automatically using portions of the second ring to create a new complete ring. A major advantage of FDDI is its high speed. It operates over fiber optic cable at 100 Mbps.
ATM
Asynchronous Transfer Mode (ATM) is a network protocol that transmits data at a speed of 155 Mbps and higher. ATM works by transmitting all data in small packets of a fixed size; whereas, other protocols transfer variable length packets. ATM supports a variety of media such as video, CD-quality audio, and imaging. ATM employs a star topology, which can work with fiber optic as well as twisted pair cable.
ATM is most often used to interconnect two or more local area networks. It is also frequently used by Internet Service Providers to utilize high-speed access to the Internet for their clients. As ATM technology becomes more cost-effective, it will provide another solution for constructing faster local area networks.
Gigabit Ethernet
The latest development in the Ethernet standard is a protocol that has a transmission speed of 1 Gbps. Gigabit Ethernet is primarily used for backbones on a network at this time. In the future, it will probably also be used for workstation and server connections. It can be used with both fiber optic cabling and copper. The 1000BaseTX, the copper cable used for Gigabit Ethernet, became the formal standard in 1999.
Compare Network Protocols
| Protocol | Cable | Speed | Topology |
| Ethernet | Twisted Pair, Coaxial, Fiber | 10 Mbps | Linear Bus, Star, Tree |
| Fast Ethernet | Twisted Pair, Fiber | 100 Mbps | Star |
| LocalTalk | Twisted Pair | .23 Mbps | Linear Bus or Star |
| Token Ring | Twisted Pair | 4 Mbps - 16 Mbps | Star-Wired Ring |
| FDDI | Fiber | 100 Mbps | Dual ring |
| ATM | Twisted Pair, Fiber | 155-2488 Mbps | Linear Bus, Star, Tree |
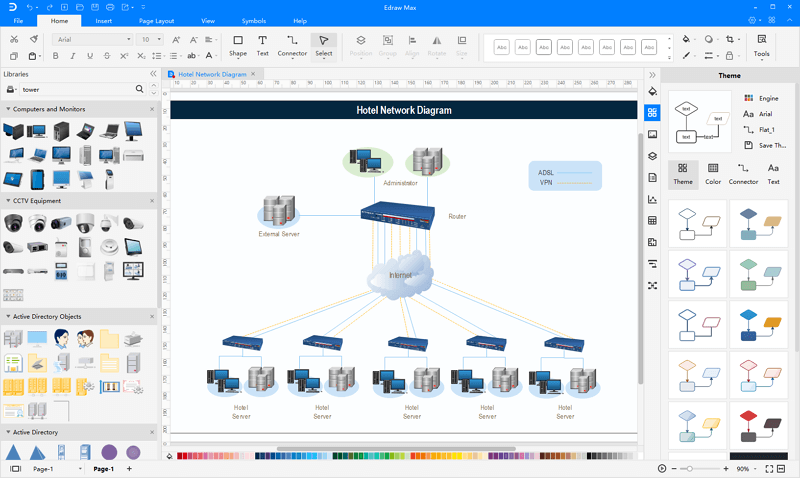
Network Diagram Software
Edraw Network Diagram software is an excellent and powerful network design tool for network drawings with diversified examples and symbols that are pre-made in Edraw libraries. So it has become quite easy and quick to draw network topologies, Cisco network design diagrams, LAN/WAN diagrams, network cabling diagrams, active directory diagrams, and physical network diagrams.
Network Protocol Overview
The OSI model, and any other network communication model, provides only a conceptual framework for communication between computers, but the model itself does not provide specific methods of communication. Various communication protocols define actual communication. In the context of data communication, a protocol is a formal set of rules, conventions, and data structure that governs how computers and other network devices exchange information over a network. In other words, a protocol is a standard procedure and format that two data communication devices must understand, accept, and use to be able to talk to each other.
In modern protocol design, protocols are "layered" according to the OSI 7 layer model or a similar layered model. Layering is a design principle that divides the protocol design into many smaller parts, each part accomplishing a particular sub-task and interacting with the other parts of the protocol only in a small number of well-defined ways. Layering allows the parts of a protocol to be designed and tested without a combinatorial explosion of cases, keeping each design relatively simple. Layering also permits familiar protocols to be adapted to unusual circumstances.
The header and/or trailer at each layer reflects the structure of the protocol. A lengthy document often defines detailed rules and procedures of a protocol or protocol group. For example, IETF uses RFCs (Request for Comments) to define protocols and updates to the protocols.
These protocols were defined by many different standard organizations throughout the world and by technology vendors over the years of technology evolution and development. One of the most popular protocol suites is TCP/IP, which is the heart of Internetworking communications. The IP, the Internet Protocol, is responsible for exchanging information between routers so that the routers can select the proper path for network traffic. At the same time, TCP is responsible for ensuring the data packets are transmitted across the network reliably and error-free. LAN and WAN protocols are also critical protocols in network communications. The LAN protocols suite is for the physical and data link layers of communications over various LAN media such as Ethernet wires and wireless radio waves. The WAN protocol suite is for the lowest three layers and defines communication over various wide-area media, such as fiber optic and copper cables.
Network communication has slowly evolved. Today's new technologies are based on the accumulation over years of technologies, which may be either still existing or obsolete. Because of this, the protocols which define network communication are highly inter-related. Many protocols rely on others for operation. For example, many routing protocols use other network protocols to exchange information between routers.
In addition to standards for individual protocols in transmission, there are now also interface standards for different layers to talk to the ones above or below (usually specific operating system). For example, Winsock and Berkeley sockets between layers 4 and 5; NDIS and ODI between layers 2 and 3.
The protocols for data communication cover all areas, as defined in the OSI model. However, the OSI model is only loosely defined. A protocol may perform the functions of one or more of the OSI layers, which introduces complexity to understanding protocols relevant to the OSI 7 layer model. In real-world protocols, there is some argument as to where the distinctions between layers are drawn; there is no one black and white answer.
To develop a comprehensive technology that is useful for the industry, a group of protocols is required in the same layer or across many different layers. Different protocols often describe different aspects of a single communication; taken together, these form a protocol suite. For example, Voice over IP (VOIP), a group of protocols developed by many vendors and standard organizations, has many protocols across the 4 top layers in the OSI model.
Protocols can be implemented either in hardware or software or a mixture of both. Typically, the lower layers are implemented in hardware, with the higher layers being implemented in software.
Protocols could be grouped into suites (or families, or stacks) by their technical functions, or origin of the protocol introduction, or both. A protocol may belong to one or multiple protocol suites, depending on how you categorize it. For example, the Gigabit Ethernet protocol IEEE 802.3z is a LAN (Local Area Network) protocol, and it can also be used in MAN (Metropolitan Area Network) communications.
The IETF designs the most recent protocols for Internetworking communications and by the IEEE for local area networking (LAN) and metropolitan area networking (MAN). The ITU-T contributes mostly to wide-area networking (WAN) and telecommunications protocols. ISO has its own suite of protocols for internetworking communications, which is mainly deployed in European countries.
More Related
Free Neural Network Diagram Examples